Ask an Expert: History Repeated with Another T-Mobile Data Breach
T-Mobile has been in the headlines often for all the wrong reasons – multiple data breaches that have affected millions of customers. The telecom giant has a history of struggling to keep its users’ information safe. Understandably, these events caused an uproar among customers, and they were quick to demand answers and improved security measures. Keep reading for a look into the history of T-Mobile data breaches, the most recent 2023 T-Mobile Data Breach and how it affected current and prospective customers, and statements from our Director of Cybersecurity.
The Summarized History of T-Mobile’s Data Breaches
Since 2018, nine hacks have been disclosed by T-Mobile, with half being in the last three years. These previous breaches ranged from the following:
2018-2020
- August 2018: About 3% of customers (2.3 million) were affected by unauthorized access to personal customer data, including the name, billing zip code, phone number, email address, account number, and account type of users.
- November 2019: Less than 1.5% of customers (over a million) were affected by unauthorized access to name, billing address, phone number, account number, rate, plan, and calling features (such as paying for international calls).
- March 2020: Unknown amount of customers affected by unauthorized access to names and addresses, phone numbers, account numbers, rate plans, and billing information.
2021-2023
- January 2021: Less than 0.2% of customers were affected by unauthorized access to name, phone number, account number, and billing address.
- February 2021: Unknown amount of customers were affected with unauthorized access to names, addresses, email addresses, account numbers, social security numbers (SSNs), account personal identification numbers (PIN), account security questions and answers, date of birth, plan information, and the number of lines subscribed to their accounts.
- August 2021: 40 million former or prospective customers affected with unauthorized access to names, date of birth, SSN, and driver’s license/ID information, were compromised. 7.8 million customers were affected by unauthorized access to name, date of birth, SSN, and driver’s license/ID information, as well as 5 million customers affected with unauthorized access to phone numbers, as well as IMEI and IMSI information.
- December 2021: “A very small amount of customers” experienced SIM Swap Attacks – meaning a SIM card assigned to a mobile number on their account may have been illegally reassigned or limited account information was viewed.
- April 2022: Stolen source code after T-Mobile employees’ credentials were stolen online. No government or customer data were compromised.
- January 2023: In November 2022, 37 million customers were affected by unauthorized access to name, billing address, email, and phone number. This breach wasn’t discovered until months later, in January 2023.
Although this list may seem extensive, it doesn’t include other bugs and vulnerabilities discovered at T-Mobile over the years.
2023 T-Mobile Data Breach: T-Mobile’s Response
After the most recent breach earlier this year, T-Mobile wrote in its SEC disclosure that since 2021, they have made a “substantial multi-year investment working with leading external cybersecurity experts to enhance our cybersecurity capabilities and transform our approach to cybersecurity.” They state that they’ve made substantial progress since and backed their statement by pledging $150 million toward enhancing their cybersecurity.
All things considered, we can only hope to see the results and benefits of their cybersecurity improvements, as T-Mobile claims that protecting customer data is their top priority.
Potential Impacts On Current and Prospective T-Mobile Customers
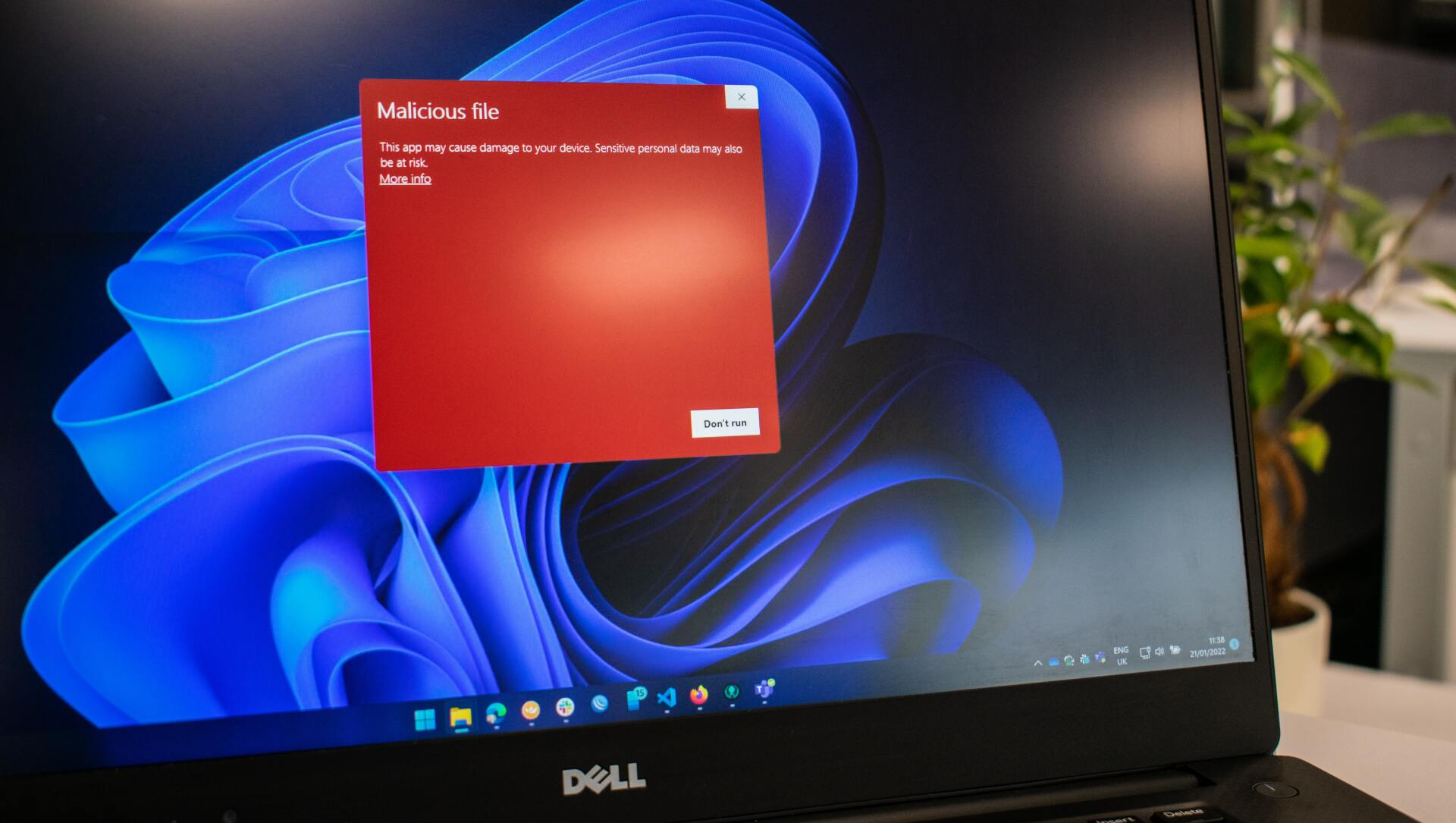
The latest data breach by T-Mobile will likely negatively impact current and prospective customers. As news of the recent breach spreads and more awareness is made about T-Mobile’s long history of breaches, people may have become wary of trusting their personal information with T-Mobile and may take their business elsewhere. It may also cause some customers to question the overall security of T-Mobile’s systems, and as a result, they may choose not to use their services.
It can be challenging to trust a company that has had multiple data breaches in its history. Still, it’s important to remember that T-Mobile has taken immediate action following its numerous breaches. They invested heavily in improved security measures and are now working to enhance their cybersecurity.
Class Action Lawsuit for January 2023 T-Mobile Data Breach
T-Mobile isn’t the first organization to suffer multiple breaches over the years, and it certainly won’t be the last. Though T-Mobile has acted quickly over the years to shut down breaches, address customers’ concerns, and offer settlements. A recent Class-Action Lawsuit was filed against them for the most recent breach announced in January 2023 breach. The lawsuit states, “T-Mobile failed to exercise “reasonable care” in safeguarding the private information of millions of consumers from a data breach announced around January 20, 2023.” Learn more about the class action lawsuit here.

The Future of T-Mobile After Its Numerous Data Breaches
The 2023 T-Mobile data breach and the prior breaches have been unfortunate events that left many of its customers feeling violated over the years. Though events like these are unprecedented, it becomes a bit concerning when they repeatedly occur to a company of this size. Since its most significant breach in 2021, T-Mobile has announced its efforts to enhance cybersecurity by pledging $150 million toward the cause and working with leading cybersecurity experts to transform its approach to cybersecurity. We have seen quick responses after past breaches and hope to see improvement in the future.
Ask An Expert: FAQ with Edge Networks’ Director of Cybersecurity
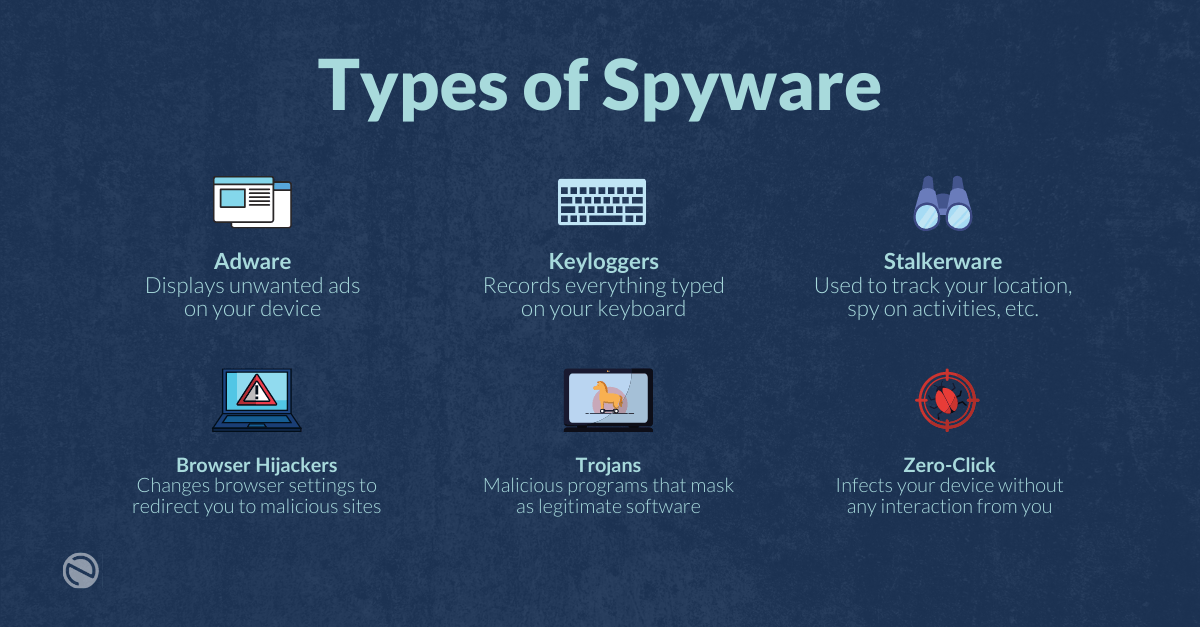
What are the most common causes of data breaches?
This is a great question; I believe that the most common causes of data breaches are misconfigurations and human error. Specifically, ensuring that MFA is enabled, and if not, that is considered misconfiguration. An example of human error would be to accept a request asking for approval to allow login if it is not actually you requesting the access.
T-Mobile has disclosed nine hacks since 2018. Why does it keep happening?
Very tough to say. T-Mobile is a national carrier with a lot of information, which makes its organization a desirable target. Cybersecurity is not one-size-fits-all. The best an organization can do is ensure they’re following a well-established security framework and aligning themselves with it.
Should I switch providers if my current one has suffered a data breach?
Honestly, one would probably run out of options if you tried that. A lot of organizations have been breached. I personally do not believe you have to switch providers. However, I also do not believe an organization is more secure after a breach than before.
How can I determine if a company is trustworthy and will handle my data safely?
This is a most excellent question! Ask the company if they have a SOC2 type 2 report that they can share. If they don’t, and the data you plan on having them work with is critical, you might consider walking away. If more consumers asked businesses for this information, they would work towards achieving a higher cybersecurity posture.
How can organizations protect themselves from data breaches?
Treating cybersecurity investments as if they were the paper your organization needed to operate. Cybersecurity should never be an afterthought, and organizations need to prepare and budget.
- Establish a security framework, and work towards “checking” all the boxes.
- Ensure that you have security awareness training for all
- Setup Multi-Factor Authentication (MFA)
- Work with partners that can help secure and align your business
How should organizations respond after a data breach?
All organizations should be 100% TRANSPARENT. Many laws are coming down the pipeline for organizations. In fact, a few states that already have stronger notification laws in place, such as California. It’s not unrealistic to believe several others will be following their lead. Work on the plan that was hopefully implemented before the breach occurred.
Conclusion
For many people, the latest T-Mobile data breach has left them concerned and vulnerable. If you have any questions or concerns, feel free to contact us. We’d love to chat with you!