Keep Your IT Humming with These Cyber Hygiene Tactics
Maintaining a healthy and secure IT environment is crucial for any organization. Just like practicing good personal hygiene keeps us healthy, adopting strong cyber hygiene tactics ensures the smooth functioning of your IT infrastructure. Whether you’re a small business owner or part of a large enterprise, implementing these eight essential cyber hygiene tactics will help keep your IT humming and safeguard your valuable digital assets.
Server and Network Management Basics
Server and network management can be a daunting task for many, regardless of administrative experience.
There are a few key baseline areas to focus on as you mature through IT progression.
First Things First
The management of your devices should begin as soon as they hit the loading dock. It all starts with asset management.
Asset Management
Asset management should be at the core of your management strategy. Asset management documentation should contain, at a minimum:
– Location of the device
– Device manufacturer
– Serial number of the device
– Warranty information
– System owner contact information
– System administrator contact information
Other good items to include:
– Base Operating system version
– Hardware installed such as CPU, RAM and port capacities, installed and available
– ROM or BIOS version and configuration
This data can assist in planning device lifecycles and when doing financial allocation and depreciation. It can be held in something as simple as a spreadsheet or as complex as an asset management system.
Configuration Management
Configuration management is just what you might think. It is the collection of the past and present configuration of a device. This data is typically managed with a configuration management database or system. It contains items such as:
– Operating system version and patch levels
– Third-party applications and plug-ins and version
– Hardware configuration including RAM, CPU, Network Interface Cards (NIC) and other installed components.
– IP addresses
– Connected devices
– Switch port speeds and duplex
The list of items tracked, known as Configuration Items (CI), should include everything so that you can effectively and efficiently manage your devices.
Why is this data important? It is important because it helps you ensure your systems are up to date. It can help troubleshoot a problem caused by a recent change or assist during a disaster when you need to replace and recover a failed component.
Change Management
Change is the addition, modification or removal of anything that could affect your IT devices and services. Change management is the process (the rules) that governs how change happens.
The scope of change management should include all IT services, CI’s, technical processes and related documentation. This data is stored in a change management database (CMDB).
Any changes made in the environment should start with a Request for Change (RFC). An RFC is a formal proposal for a change to be made in change management. An RFC includes all the details of a proposed change and can be recorded by either paper or electronic means. More mature organizations use software tools to track and manage these requests.
Types of Change
There are three main types of change in change management: Standard Change, Normal Change, and Emergency Change.
Standard Change
A standard change is a pre-approved change that is low risk, relatively common and follows a defined procedure or work instructions. For instance, the password change of a user every three months is a good practice. It is common, and when the user follows the instructions, they can change the password easily.
Standard changes do not require an RFC to be submitted. Standard changes are logged and tracked using different mechanisms within the change management process. These changes are typically logged as a service request and are managed by the service desk.
Normal Change
Normal change is every change that is not classified as a standard or emergency change. If a new feature has been introduced for a new service or existing service has been updated, this is an example of a normal change. For instance, a software update or addition is an example of normal change classified in change management.
Emergency Change
The third type of change is emergency change. Instead of extending an existing service or introducing a new service, emergency changes are initiated generally to solve a major incident or implement a security patch. Emergency changes must be introduced as soon as possible. For example, if a security exploit has been identified that can harm the company, customer data, or reputation due to data loss or leakage, this is a critical issue and must be fixed immediately.
The change management process will normally have a specific procedure for handling emergency changes. Normal change procedure can be more bureaucratic and can take time to get all approvals to implement them, but because since emergency changes must be implemented as soon as possible, there can be faster and specific procedures or checklists for handling emergency changes.
Catch a CAB
Good Cyber Hygiene Tactics to Implement
Last, but certainly not least, it is important to remember to take care of small housekeeping details to keep your devices humming. Here are some critical but easy ones.
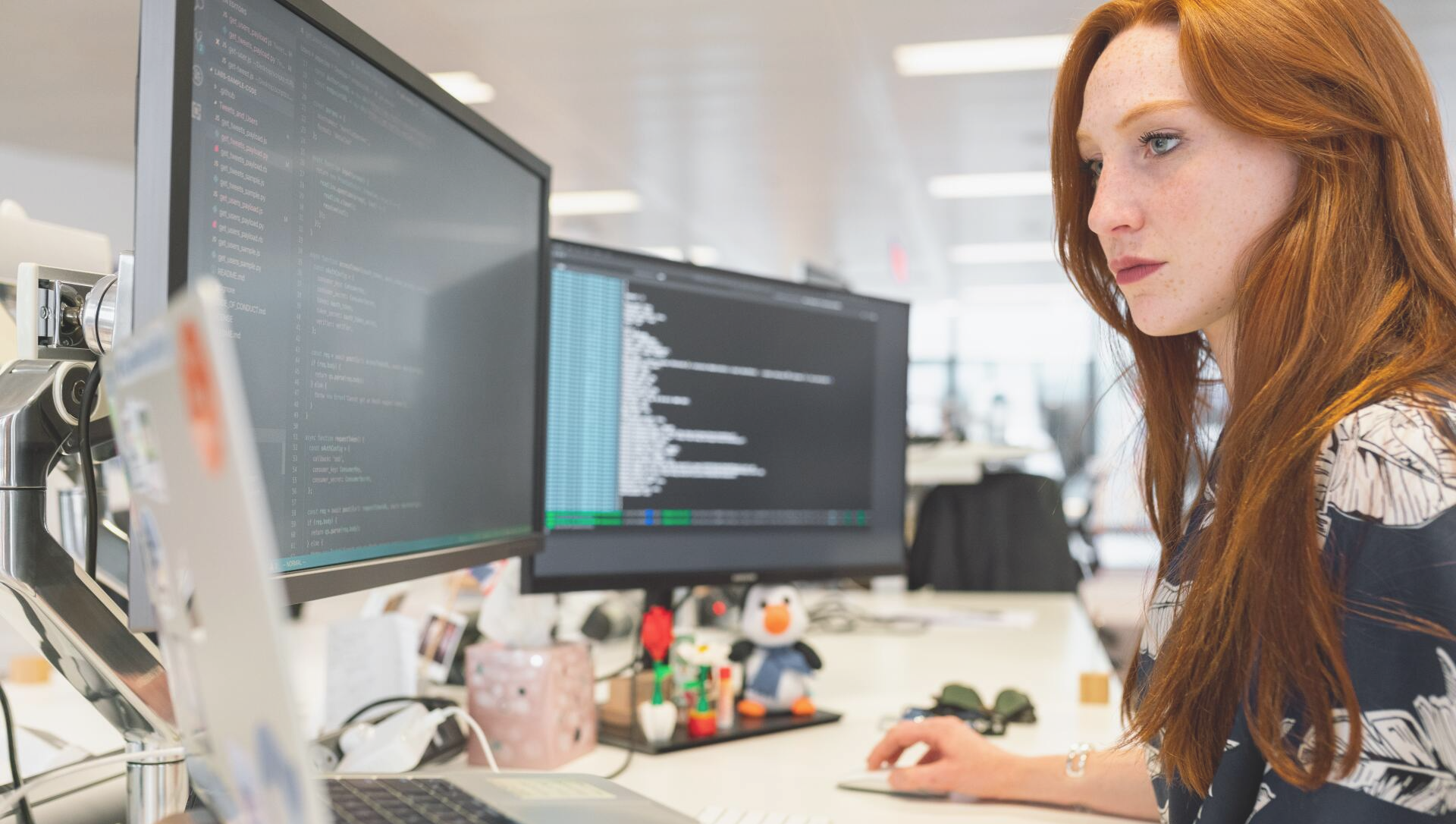
1. Review logs – Check logs on your devices to ensure that the system and security are not providing obvious red flags. Having an event monitoring tool makes this task easy and provides granularity on important events occurring.
2. Archive logs – Logging takes up a lot of space. Ensure that you save these logs to long-term storage regularly so you can still review them if needed.
3. Maintain separate admin accounts – Do not give administrative privilege to an administrator’s daily account. Assign complex passwords and controls to these accounts. On devices, create accounts specific to that device for both reporting and administrative functions.
4. Service accounts – Create separate service accounts on servers that are members of the domain and not local. Ensure a complex password is used, and proper controls to the accounts are followed.
5. Antivirus/AntiMalware – If possible, use centralized management and reporting for this software. Aside from real-time protection, make sure to schedule a routine task to do a deep scan.
6. Service packs, patches and updates – Threats are evolving on an hourly basis. Have a process or use a tool that keeps your devices in sync with the latest critical updates.
7. Device monitoring – Use the manufacturer’s tools or consolidated monitoring to know when devices are down, have heavy RAM or CPU use, run out of storage space, or experience network flooding.
8. Backup critical data – Perform regular backups of your data and system states. Keep local and offsite/cloud-based copies of this data in the event you may need to restore.
As you have read, both documentation and good operational discipline are mainstays to a more reliable and predictable IT environment. It is never too late to start implementing good cyber hygiene tactics, and the process is continuous.
We at Edge Networks know that when managing your IT, there can be a lot of moving parts and potential pitfalls Remove the burden of managing your IT with our flat-fee IT managed services program. Contact us to schedule a free, 30-minute consultation today.