Mission Possible: How to Remediate the Cybersecurity Leadership & Strategy Resource Pain Through a vCISO Program
This is a continuation of our series about the value and importance of aligning your company’s cybersecurity program with your corporate mission. In the previous blog, I addressed the meaning of aligning a company’s cybersecurity program with your mission, along with its value and importance. Additionally, high-level practical strategies and tactics were provided to make the alignment possible.
In this blog, I will explore one of those key tactics, implementing a vCISO (Virtual Chief Information Security Officer) program – and how it helps Edge Networks’ customers remediate one of their key business pains today – a lack of cybersecurity leadership and strategy resources. In doing so, I will share how our corporate mission statement, “to enhance our customers’ business resiliency through simplified cybersecurity,” originated and how it applies to helping our customers remediate their cybersecurity pains.
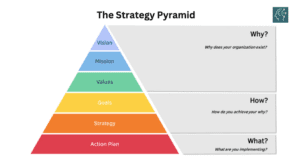
When Mark Tishenko, Edge Networks’ Founder and CEO, and I decided to work together to lead the company, one of our first priorities was to evaluate Edge’s corporate mission and determine how to best move the company forward through it. We both recognized the importance of the company’s mission statement and why it sits on top of our strategic pyramid – to provide a clear, unifying purpose and direction for the organization. We agreed that our mission statement serves as a constant reminder of why our company exists and ensures that all strategic initiatives and decisions are aligned with this overarching mission.
With that in mind, we thoughtfully selected this mission statement for Edge Networks: “to enhance our customers’ business resiliency through simplified cybersecurity.” We were unified in our belief that this communicates the essence of what we do well and concisely defines who we are and why we exist. It also clearly articulates the importance of cybersecurity – simplified cybersecurity – to our customers’ long-term success.

A significant part of the process of establishing our mission statement was answering this question, “how will we accomplish our mission?” Answering that question required focusing on the most important elements of our customers’ decision criteria and processes regarding their organizations’ well-being and cybersecurity’s role in it. What drives our customers’ decisions on their approach to cybersecurity and its impact on organizational resiliency? What cybersecurity challenges do our customers need to address? What cybersecurity problems do they need to solve? What keeps them up at night? Ultimately, it boils down to this question – what are our customers’ key business and cybersecurity pains?
An organization’s business pains can refer to the specific challenges, problems, or issues that it faces in its day-to-day operations or strategic goals. These pains can vary widely depending on the nature of the business, industry, and external factors. Identifying and addressing these business pains is essential for an organization’s growth, efficiency, and overall success.
One of the most prominent pains that every organization faces today is cybersecurity. Specifically, cybersecurity pains refer to challenges, vulnerabilities, and issues that an organization faces in safeguarding its digital assets. These challenges can vary widely depending on the organization’s size, industry, technology infrastructure, and the evolving nature of cyber threats. Identifying and addressing cybersecurity pains is essential for maintaining operational continuity and safeguarding the organization’s reputation.
By understanding our customers’ business and cybersecurity pains and focusing on delivering solutions that remediate those pains in the most effective, efficient, and simplest way possible, Mark and I were confident that Edge Networks will be very successful in accomplishing our mission.
What that in mind, we developed a list of the most common cybersecurity pains that many organizations are dealing with today. Our list included the following pains:
- Data Breaches: Incidents where unauthorized individuals gain access to sensitive data, such as customer information, financial records, or intellectual property, can result in significant damage.
- Malware and Ransomware: Dealing with the constant threat of malware, including ransomware attacks that can encrypt data and demand a ransom for decryption.
- Phishing and Social Engineering: Employees falling victim to phishing emails and social engineering scams can lead to data breaches and compromise security.
- Weak Authentication and Password Policies: Managing user authentication and enforcing strong password policies can be challenging, especially in large organizations.
- Insider Threats: Concerns related to employees or contractors intentionally or unintentionally compromising security by leaking sensitive data or engaging in malicious activities.
- Patch Management: Ensuring that all software and systems are up-to-date with the latest security patches to mitigate vulnerabilities is an ongoing challenge.
- Compliance and Regulatory Requirements: Meeting industry-specific cybersecurity regulations and compliance standards can be complex and costly.
- Limited Resources: Resource constraints and lack of qualified cybersecurity personnel and technologies.
- Third-Party Risk: Managing and assessing the cybersecurity risks associated with third-party vendors, suppliers, and partners.
- Incident Response: Developing and maintaining an effective incident response plan to address cyber incidents promptly.
- Security Awareness Training: Ensuring that employees are educated about cybersecurity best practices and threats requires ongoing effort.
- Shadow IT: Managing the use of unauthorized or unapproved software and services within the organization’s network.
- Mobile Device Security: Securing mobile devices used by employees and ensuring they don’t become entry points.
- Scalability: Adapting cybersecurity measures to accommodate the organization’s growth and changing technology landscape.
Since simplicity – specifically, simplified cybersecurity – is a core component of our mission, we recognized the need to break down, consolidate, and integrate the above list. In other words, we needed to simplify it.
This exercise resulted in our decision to classify our target customers’ pains into three core categories:
Cybersecurity Operations: Remove operational resource constraints and improve outcomes.
Governance, Risk, & Compliance: Eliminate inefficient GRC processes – and spreadsheets.
Leadership & Strategy: Increase leadership resources, and align cybersecurity with your company’s mission and strategy.

The next step is to identify the tactical solutions that Edge Networks offers to remediate the pains within those three pillars. While there are a lot of solutions that we can offer to customers for each of the pain pillars, we determined that we should focus on the core solutions that will deliver the most value to our customers, and where we will excel at delivering the most. Once again, we endeavored to simplify, which resulted in selecting and organizing our service menu this way:
- Threat Monitoring & Detection
- Vulnerability Management
- Incident Response
- Security Awareness Training / Phishing
Governance, Risk, & Compliance:
The top pain pillar is Leadership & Strategy, and vCISO is the first tactical solution listed. This is intentional. Effective leadership in cybersecurity and the development of a comprehensive cybersecurity strategy are a priority because they protect an organization’s assets, reputation, and financial well-being while identifying, managing, and minimizing business pains associated with cyber threats and challenges. Taking a proactive leadership stance by integrating cybersecurity into the fabric of the organization increases the protection of the company’s assets, reputation, and long-term success. Proactive cybersecurity leadership is an investment in an organization’s long-term success and resilience. As the saying goes, “it starts with leadership”, and cybersecurity is no different.
Up to this point, Mark and I – with a lot of help from our outstanding Go to Market team – could check these items off our list:
- Established our corporate mission statement.
- Addressed how we will accomplish our mission (by relieving our customers of their most critical cybersecurity pains).
- Identified how to classify and categorize our solutions to address our customers’ pains in the most meaningful, easy-to-understand, and simplest way possible.
The next important step was to ensure that the description and details about our services were comprehensive, meaningful, and applicable to our customers. This is a big project, and we needed a lot of assistance and collaboration from our Go-To-Market team to complete it well. Once again, the team came through, above and beyond expectations.
With respect to vCISO, we determined that the key components of the program were the following:
- It is a service that provides our customers with access to experienced cybersecurity professionals who act as virtual or outsourced CISOs.
- It is a strategic cybersecurity initiative that assists our customers in enhancing their security posture, aligning cybersecurity with their mission and strategy, and leveraging external expertise to address the complexities of today’s cybersecurity landscape.
- It provides a flexible and scalable solution to our customers to bolster their cybersecurity leadership and capabilities.
Furthermore, we concluded that the primary goal of our vCISO program is to enhance our customers’ cybersecurity posture and strategy by offering specialized expertise and leadership in the following ways:
- Increased Leadership Resources. Organizations often struggle to find and retain qualified cybersecurity professionals, especially for executive-level roles like CISO. Our program addresses this challenge by providing access to a virtual CISO who brings a wealth of experience and expertise to the table. This augments our customers’ leadership resources without the need for a full-time, in-house CISO. Employing a full-time CISO can be expensive. A vCISO program offers a cost-effective alternative, allowing our customers access to top-tier cybersecurity leadership without the high overhead costs associated with a full-time executive.
- Alignment with Mission and Strategy. We work closely with our customers’ leadership team to understand its mission, goals, and strategic objectives. By aligning cybersecurity efforts with the broader mission and strategy of the organization, the vCISO helps ensure that security initiatives are in sync with the company’s overarching priorities.
- Cybersecurity Expertise. Our vCISO is an experienced cybersecurity professional who can assess our customers’ current security posture, identify vulnerabilities and threats, and recommend appropriate security measures. We bring best practices and industry knowledge to our customers, helping them stay ahead of emerging threats.
- Risk Management. Our vCISO plays a crucial role in risk management. We assist in identifying and quantifying cybersecurity risks, developing risk mitigation strategies, and helping our customers prioritize security investments based on the potential impact on the mission and strategy.
- Compliance and Regulation. Many industries are subject to specific cybersecurity regulations and compliance requirements. Our vCISO helps ensure that our customers adhere to these regulations and maintain compliance, reducing the risk of penalties and reputational damage.
- Cybersecurity Program Development. We assist in developing a comprehensive cybersecurity program tailored to our customers’ needs. This includes policies, procedures, incident response plans, and security awareness training.
- Incident Response. In the event of a cybersecurity incident or breach, our vCISO provides guidance and expertise in managing the incident effectively, minimizing damage, and facilitating recovery.
To further establish credibility and confidence with our current and prospective customers, backing up our service claims with evidence through real customer use cases is important. Fortunately, Edge was in a good position in this area. For example, we were already delivering services to customers in a very similar manner as described in the vCISO service description above.
One of those customers is a food service company that employs more than 1,000 employees. This customer needed a vCISO to help remediate several pain points, including:
- Insufficient cybersecurity leadership and strategic resources
- Lack of a centralized GRC management platform and integrated operational processes
- Insufficient incident response program
- Misalignment between cybersecurity mission and strategy
- Immature cyber risk management program
- Gaps in communication with executive leadership and board members regarding cybersecurity strategy and initiatives
- Ineffective cybersecurity maturity program
To remediate those pains, we are delivering a comprehensive vCISO solution to this customer, which includes the following components:
- Comprehensive vCISO services for proactive cybersecurity leadership and resilience
- Strategic leadership
- GRC leadership w/ EdgeGRC platform
- Cybersecurity maturity roadmap
- Vendor & third-party risk management
- Security technology evaluation
- 25 hours per month of Edge vCISO time
As part of the vCISO program, Edge’s vCISO is delivering EdgeGRC as an integrated solution for streamlined compliance management. This solution includes:
- Turnkey NIST CSF framework alignment
- Unified dashboard and reporting
- Automated workflow and task management
- External collaboration and sharing
- Up to 1 additional custom framework alignment
The results have been spectacular. Our customer’s engagement with our vCISO program has led to a substantial improvement in their cybersecurity posture and strategy. By leveraging the expertise of virtual cybersecurity leadership, our customer not only enhanced their security measures but also benefited from cost savings, compliance adherence, and improved relationships with stakeholders. Edge’s vCISO program has become a valuable asset in strengthening our customer’s overall cybersecurity resilience and success.
Our customer featured in the above use case is experiencing improved alignment of their company’s cybersecurity program with their corporate mission. This is happening because of increased awareness within their organization about the meaning of aligning their cybersecurity program with their mission, along with its value and importance.
Additionally, they have benefited from partnering with us to receive practical strategies and tactics to make the alignment more possible. One of those strategic key tactics is implementing Edge’s vCISO program, which has helped remediate one of their key business pains – a lack of cybersecurity leadership and strategy resources. In doing so, they are helping Edge Networks fulfill our corporate mission statement, “to enhance our customers’ business resiliency through simplified cybersecurity”.
The vCISO program is one of several remediation solutions that Edge offers to our customers for the leadership and strategy pain pillar. The other two pain pillars, Cybersecurity Operations & Governance and Risk & Compliance, have several remediation solutions within each of them as well. I look forward to examining all the pain pillars and remediation solutions in future blogs.