Protecting Yourself in the Digital World
In today’s interconnected digital landscape, where online transactions and collaborations are the norm, it’s important to be aware of the various threats lurking in the shadows. Vendor Fraud is one of the latest financial scams and can occur from one or multiple sources in a very sophisticated manner. If not detected, it can cost businesses severely.
What is Vendor Impersonation Fraud?
Vendor Impersonation Fraud is a form of Business Email Compromise fraud that occurs when a malicious actor or employee scams a company into making payments to fraudulent accounts. This can happen in multiple ways, such as providing fake vendor or account information, hijacking a vendor or employee’s email account, or pretending to be a reliable vendor with the intention of carrying out fraudulent activities, such as invoice scams or other forms of financial fraud.
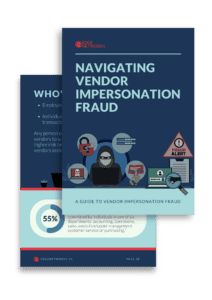
Third-party impersonations made up 52% of all Business Email Compromise (BEC) attacks in May 2022, but keep in mind unaffiliated malicious actors aren’t the only ones committing fraud; they can be employees as well. In fact, more than 55% of frauds were committed by individuals in one of six departments:
- Accounting
- Operations
- Sales
- Executive/Upper Management
- Customer Service
- Purchasing

Types of Vendor Impersonation Fraud
There are many types of vendor impersonation fraud, but these are the most common:
- Cyber Fraud cases involving unauthorized individuals who have no affiliation with the company or the vendor are among the most challenging to identify. These malicious actors manipulate the account of a trusted vendor, redirecting payments to their own accounts electronically. Every quarter, 2/3 of all organizations are targeted by email attacks that use a compromised or impersonated third-party account.
- Check Manipulation involves an individual forging or modifying information on a vendor’s check to route payments to a personal bank account.
- Ghost Vendor occurs when a fictitious vendor is created in the company’s records. Payments are then made to this non-existent vendor, and an employee or an external fraudster usually siphons off the funds.
- Duplicate Payments occur when an employee uses a legitimate vendor’s account, manipulates the payment records, and initiates multiple payments for a single vendor invoice in order to direct the second payment to their personal account.
Who’s at Risk of Vendor Impersonation Fraud?
While anyone can potentially fall victim to vendor impersonation fraud, certain individuals and organizations are more susceptible to these scams, such as those that handle finances. These are the primary targets for vendors seeking to exploit payment processes.
- Small businesses or organizations with limited resources and cybersecurity measures in place are often targeted due to their perceived vulnerability.
- Organizations with a high volume of vendor interactions or those engaged in frequent international transactions may be more exposed to vendor impersonation fraud attempts.
- Employees in accounts payable departments
- Individuals responsible for making financial transactions
How to Identify Vendor Impersonation Fraud?
In 2020, the average fraud scheme lasted a median of 18 months before being detected, which is why it’s critical to know what to look for.
- Discrepancies in Vendor Information: Review vendor details such as contact information, addresses, or tax identification numbers. Be wary of inconsistencies or if the information provided cannot be verified.
- Unusual Payment Requests: Beware payment requests that deviate from standard procedures, including sudden changes in bank account details, requests for expedited payments, or requests for payment to unfamiliar or unrelated third-party accounts.
- Inconsistencies in Invoices or Documentation: Scrutinize invoices for irregularities, such as misspellings, incorrect formatting, or missing information. Fake or altered invoices are common signs of fraudulent activity.
- Suspicious Communication Patterns: Pay attention to any sudden changes in how your vendor communicates with you, like using different email addresses, unusual phone calls, or requests to communicate outside of normal channels.
- Unexpected Price Increases: Be cautious if there are significant and unexplained price increases from a vendor. Fraudsters may attempt to overcharge for products or services, hoping to slip unnoticed.
- Poor Quality or Undelivered Goods/Services: If you receive substandard goods or services or if your orders consistently go unfulfilled, it could be a red flag for vendor fraud.
- Unusual Vendor Behavior: Be alert to vendor behavior that deviates from their usual practices, including evasive answers, sudden unresponsiveness, or reluctance to provide documentation or clarification.
- Stay Informed: Keep up-to-date with fraud trends and news within your industry. Awareness of new tactics and scams can help you be more proactive in identifying vendor fraud. Be sure to educate your employees on vendor impersonation fraud and encourage them to report suspicious activity. They may notice irregular vendor interactions or uncover information that could help identify fraud.
No single indicator guarantees the presence of vendor fraud. However, being vigilant and combining multiple factors for assessment can significantly improve your ability to identify potential fraudulent activities and protect your organization from falling victim to vendor fraud.
Measures to Detect and Prevent Vendor Impersonation Fraud
Vendor Tips:
- Due Diligence: During the onboarding process, focus on verifying vendor details such as mailing addresses, contact numbers, vendor tax identification numbers, contact persons, and bank accounts. Also, check the vendor’s financial stability.
- Conduct Reputation and Reference Checks: Research the vendor’s reputation within the industry. Seek references from other clients or business partners who have worked with the vendor before. This allows you to gather insights into their reliability, integrity, and history of delivering quality services.
- Evaluate Internal Controls: Assess the vendor’s internal controls and anti-fraud measures. Review their policies and procedures related to fraud prevention, cybersecurity, and data protection. Strong internal controls demonstrate the vendor’s commitment to mitigating the risk of fraud.
Employee Tips:
- Split Responsibilities & Regular Rotation: Separating the tasks of inputting purchase information and approving transactions can help limit employee misconduct. You can also rotate duties of employees in vendor management and purchasing or rope in managers to monitor important tasks.
- Run Thorough Background Checks: Conduct thorough background checks on all employees involved in vendor management or financial transactions. Verify their credentials, employment history, and conduct reference checks to ensure they have a trustworthy track record.
- Anti-Fraud Training & Anonymous Tip Line: Provide comprehensive training to employees on fraud prevention, including specific information about vendor impersonation fraud. Additionally, encouraging your employees to report suspicious activity of their colleagues can strengthen internal controls.
Click here to download a FREE Vendor Impersonation Fraud E-Book!
System Tips:
- Invest in Vendor Management Software: Consider streamlining and automating the process of managing vendors and their relationships. A centralized platform can efficiently handle vendor onboarding, contract management, performance tracking, compliance monitoring, and more.
- Educate Your Team: Educating your team about vendor fraud risks and consequences can enhance their awareness & vigilance. Conducting regular risk assessments helps identify loopholes & vulnerabilities that should be closed to mitigate vendor fraud effectively.
- Monitor and Audit: Actively monitor vendor-related transactions and activities for any signs of suspicious behavior. Regular audits can help assess the effectiveness of existing control measures and identify any vulnerabilities that malicious actors may exploit.
How to Respond to Vendor Fraud
- Notify Authorities & Affected Parties: Report the fraud to local law enforcement agencies and provide all relevant details and evidence. Additionally, notify financial institutions and anyone directly affected.
- Document and Preserve Evidence: Gather and securely store all evidence related to the fraud, including emails, invoices, payment records, and any communication with the fraudulent party. This is crucial for investigations, insurance claims, and potential legal proceedings.
- Seek Legal and Professional Advice: Consult with legal advisors specializing in fraud and cybersecurity. They can guide you through the legal implications, advise on recovery options, and assist with any necessary legal actions against the fraudsters.
Real-World Cases of Vendor Fraud
Sometimes reading real-world examples is the best way to understand something. Below are some real-world cases of vendor impersonation fraud at large organizations, small businesses, non-profits, and even government organizations.
- Google: In 2013, a man and co-conspirators scammed Google into paying him more than $23 million using forged invoices, contracts, letters, and corporate stamps.
- Facebook: In 2015, the same man scammed Facebook out of $98 million. The payments were wired to bank accounts throughout Latvia, Cyprus, Slovakia, Lithuania, Hungary, & Hong Kong.
- Ubiquiti: In 2015, employee impersonation & fraudulent requests from an outside entity targeted Ubiquiti’s finance department resulting in a transfer of over $46.7 million.
- Toyota Boshoku Corporation: In 2019, attackers managed to convince an employee with financial authority at a major Toyota auto parts supplier to change account information on an electronic funds transfer, resulting in a loss of $37 million.
- Government of Puerto Rico: In early 2020, the finance director of Puerto Rico’s Industrial Development Company received an email explaining a change to the bank account tied to remittance payments. $2.6 million was mistakenly transferred.
- Save the Children Charity: In 2018, a well-researched attacker gained access to an employee’s email account and sent fake invoices requesting payment close to $1 million for solar panels in Pakistan, where a Save the Children Health Center was located.
Education Empowers Us
In conclusion, staying educated on vendor impersonation fraud is of utmost importance in today’s digital age. The ever-evolving tactics used by fraudsters necessitate constant vigilance and awareness. By staying informed about the latest techniques employed by scammers, individuals and businesses can better protect themselves from falling victim to fraudulent activities.
Education empowers us to recognize warning signs, question suspicious requests, and implement robust security measures. It enables us to safeguard our financial resources, personal information, and reputations. Moreover, by sharing knowledge and promoting awareness, we collectively contribute to a safer online environment for everyone. Therefore, let us remain committed to staying educated on vendor impersonation fraud and strive to outsmart the fraudsters at their own game. If you are looking for a cybersecurity professional to help you improve your organization’s cybersecurity posture, or if you have been the victim of vendor impersonation fraud and are looking for recovery options, contact us today.