Everything you need to know about Cybersecurity Consulting Services
In today’s world, cybersecurity has become incredibly important. News of major ransomware attacks and other kinds of hacking has revealed how vulnerable many businesses and even government networks really are. All it takes is one piece of code getting where it shouldn’t, and all of your business’s digital data and records are at risk. That’s where cybersecurity consulting comes in.
Cybersecurity consultants help businesses beat the threat of hacking long before a hacker tries to breach your security. We’ll cover everything you need to know about cybersecurity consulting, from what consultants do to when your business needs one. We’ll also cover the benefits of qualified outside cybersecurity consulting, so you know what to expect.
Let’s dive in.
What Is Cybersecurity Consulting?
Cybersecurity refers to the integrity of digital systems and networks from outside attacks. A secure system is difficult to access and is protected against the most recent innovations in hacking and digital spying.
Cybersecurity consultants help both businesses and private individuals keep their information and data systems as safe as possible. They expose and fix weaknesses, maintain system integrity, and may even help detect malware and other security breaches before they can cause severe damage.
Here’s how they do it:
How Cybersecurity Consulting Benefits You
Since cybersecurity consultants often work behind the scenes, it’s common for businesses and individuals not to know what their consultant is doing. Here are some of the most common tasks a cybersecurity consultant is performing and how they help.
Now, some consultants only recommend action without taking it. It all depends on what kind of consultant you’re working with. Always check to see if your consultant will be able to implement changes and perform maintenance to keep your system safe, or if they are strictly offering advice.
Staying Up To Date On Current Cyber Threats
Since there are always new viruses and new vulnerabilities in any digital system, it’s important to keep your cybersecurity measures as up-to-date as possible.
That’s part of where consultants come in. Cybersecurity consultants stay up to date on current risks and are aware of the vulnerabilities in common operating systems and data structures. That way, they can address potential threats and help push necessary updates to close any vulnerabilities.
Install and Maintain Firewall Protections
In addition to maintaining awareness of the current threats, cybersecurity consultants can install firewalls and other protections to keep your data safe. Firewalls work in conjunction with the defenses in your operating system to help prevent any incoming attack from reaching your data.
Password Authentication and Maintenance
A good cybersecurity consultant can also help ensure that all passwords used to access your data are secure and up to date. They can help with purging old passwords, as well as suggesting password protection upgrades to help keep your business’s information secure.
Helping Meet Compliance Standards
While the United States doesn’t have any enforced cybersecurity standards, it’s still a good idea to ensure your cybersecurity measures are compliant with current industry standards. Since the EU does have cybersecurity standards for business, those are the most common benchmark for good cybersecurity practices.
A cybersecurity consultant can make sure all standards are being met and that your business consistently scores well on compliance checks.
This isn’t just a great way to make sure your information is secure; it’s also good reassurance for investors and stockholders. Meeting high cybersecurity standards is the best way to convince stockholders and customers that their information is safe with your business.
Testing Vulnerabilities
Most cybersecurity experts have some idea of how to exploit cybersecurity weaknesses and how to hack into data systems. That’s important because it means that they know what hackers are looking for and what the most common vulnerabilities will be.
Testing a system’s vulnerabilities is one of the best ways to see how well protected your data is, and many cybersecurity consultants offer testing services for precisely that reason. Periodic testing is an excellent way to stay on top of any new vulnerabilities and improve the strength of your firewall and other safety measures.
Maintain Email Security
One of the most essential forms of communication for many businesses is email. Unfortunately, unsecured email can also be one of the most vulnerable parts of your business’s data network (and an easy point of entry for hackers).
Cybersecurity consultants can recommend the appropriate level of encryption, as well as password and verification standards, to help keep your network safe. That way, you can email as often as you need to, without worrying about a breach.
Mobile Security Planning
As more and more businesses rely on mobile devices and on-the-go communication, those devices are introducing another layer of necessary security. Most mobile devices are still relatively secure, with only a few known weaknesses and breaches to worry about. However, the relative security of mobile devices is changing and changing fast.
Getting ahead of possible security problems with a mobile device security plan is essential, and most cybersecurity consultants can help.
Other Security Tasks
It’s not practical to list all the benefits of having a cybersecurity consultant, or what they can do to help ensure your business’s long-term security. Don’t be surprised if your cybersecurity consultant recommends other changes (or if you see additional benefits to the ones we’ve listed here).
When Is It Time To Get A Cybersecurity Consultant?
The truth is, most people and businesses don’t know when it’s time to get a cybersecurity consultant on their side. Many businesses assume that hackers are only going to be going after the biggest companies and the most important competitors in any niche, but that isn’t true.
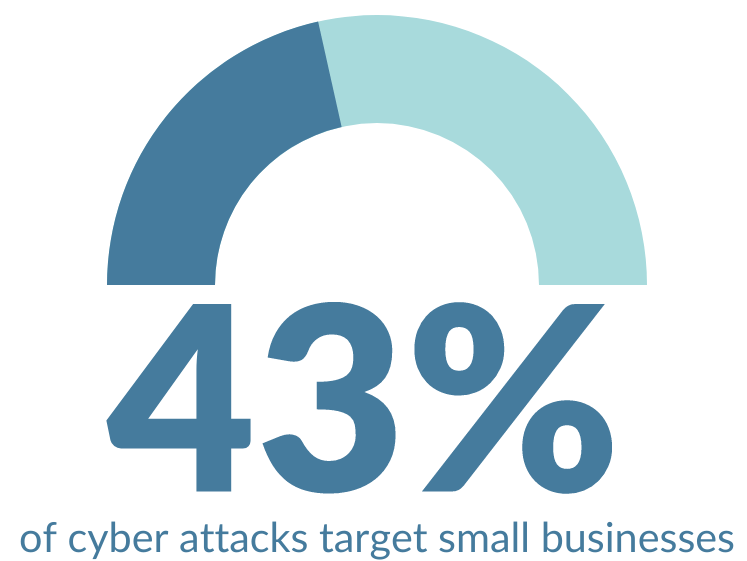
(Source: Mars Technology, 2019)
Hackers target small companies 43% of the time, according to Mars Technology. That may be because small companies tend to have less robust security systems, making them easier to target.
If you want to avoid becoming a target for hackers, you have to understand when your data might be valuable to them, and how to protect your data before hackers realize you’re a good target.
Here are some ways to tell when it’s time to hire a cybersecurity consultant.
What Kind of Business Do You Run?
Businesses often assume they have to reach a certain size before hiring a cybersecurity consultant, but the truth is that the industry they work in can be just as important.
For instance, healthcare companies should always have a cybersecurity consultant because of the kinds of information they collect from patients and clients. Similarly, law enforcement agents should always have a cybersecurity consultant or expert on staff since they also handle sensitive personal information and identification.
The more sensitive the information your business collects, the more important it is to have a cybersecurity expert available to help protect that data. One common benchmark for hiring a cybersecurity expert is if your business collects clients’ or customers’ addresses, social security numbers, or other risky personal information.
How Many People Access Your Data Network?
Another good way to tell if you need a cybersecurity consultant is how many people work with your data each day. The more people logging into your network, communicating on your email servers, or otherwise accessing your network, the more important it is to have a good consultant.
How Damaging Would A Data Breach Be?
Small businesses specifically often struggle after a data breach, whether or not their data was stolen or used maliciously. Investors and customers lose confidence in businesses after data breaches, and small businesses often struggle to raise the resources they need to recover.
The more potentially damaging a data breach would be, the more likely it is you need a cybersecurity consultant in the worst-case scenario.
Do You Know What Technologies Are Safe?
Another good sign that you might need a cybersecurity consultant is not knowing what programs and technologies are safe to use and how to secure the tools you already use.
Cybersecurity consultants can be brought in for ongoing or one-time consultations to help you choose the kind of security measures that work best with your business and help you use the most secure options.
For instance, a cybersecurity consultant might recommend what email service to use for official correspondence, or help you set up a business email server to help keep your communication safe. If you collect and store client information, they can help you choose what program and security system you need for that information.
Even if you don’t work with your cybersecurity consultant long-term, these services can help keep your business safe.
What To Look For In A Good Cybersecurity Consultant
Choosing a cybersecurity consultant can be difficult. You need someone who not only understands the finer points of cybersecurity, but also communicates them well and can gauge the needs of your business.
Other than just professional qualifications, here are a few things to look for in a good cybersecurity consultant.
They’ve Worked In Your Industry
One good sign for any cybersecurity professional is if they’ve already had experience working in your industry. Some kinds of businesses need stricter protections, while others can use mild protection effectively.
If your cybersecurity consultant has worked in your industry before, the odds are good that they’ll know what protections you need and which are good value for the industry.
It’s also a good bet if your cybersecurity professional has worked in similar industries. For instance, healthcare needs strict protections, but a consultant that has experience working with primary care doctors can likely work well with chiropractors, hospitals, and other healthcare businesses.
Reviews
Business consultants of all kinds rely on testimonials about their services, so it should be relatively easy to find reviews for any cybersecurity consultants you’re considering.
Read several of the reviews to get an idea of where this consultant excels. Reviews might tell you things like what industries they’ve worked with, what areas of specialty they have, and how well this consultant communicates with clients.
Bad reviews can also tell you a lot about a consultant. For instance, did they recommend solutions that were outside the business’s budget? Did they recommend solutions that weren’t compliant with cybersecurity standards or exceeded standards for no reason?
Do They Implement Suggestions?
Some cybersecurity consultants look over your systems, recommend improvements, and leave it to the business to implement these changes. These consultants are great if you have an established cybersecurity or IT team, since you won’t be paying the consultant for tasks your regular employees can perform.
However, suppose you don’t have your own cybersecurity team. In that case, it’s usually better to look for a full-service consultant or someone who can take your existing security measures, suggest improvements, and implement the changes after getting your approval.
You can usually tell the difference between these types of consultants by looking at the services offered on their website.
What Certifications Do They Hold?
Cybersecurity consultants typically carry several certifications to prove that they are qualified to do what they are doing. Looking for these certifications is a good litmus test to ensure your consultant can handle making security improvements.
Here are a couple of the more important and most common certifications for cybersecurity professionals.
CEH – Certified Ethical Hacker
This certification proves that your consultant knows how to hack and knows what weaknesses to look for. Holders of this certification often offer security testing services where they attempt to hack your system to look for vulnerabilities and make recommendations.
CISM – Certified Information Systems Manager
This certification is one of the most common requirements for cybersecurity professionals. Not all cybersecurity professionals hold it, but many businesses look for this credential when they’re hiring. This certification covers information systems security, security maintenance, incident management, and other critical cybersecurity skills.
CISSP – Certified Information Systems Security Professional
Issued by the ICP, this is another critical security certification that can prove your consultant has the skills to evaluate and implement a high-quality security system.
This certification is all about the design, implementation, and maintenance of top-notch cybersecurity systems. It’s an excellent qualification to look for you if you’re looking for a custom-created cybersecurity system, but not necessary for implementing basic firewalls and encryption.
Are you ready to take the next steps in ensuring your business’s cybersecurity? Edge Networks is here to help. Get started with an IT Risk Assessment, or contact us today for a free 30 minute consultation.